Trezor Login — Access Your Wallet with Confidence
A clean, elegant guide to logging in and authenticating with your Trezor hardware wallet — visual cues, secure steps, and a unique interface concept to make the process intuitive and trustworthy.
Hardware-first
On-device confirm
🔐
Secure Login
What the login does
Logging in pairs your Trezor device with the Trezor Suite (desktop) or a compatible wallet interface. Authentication is unique: approvals happen on the physical device, ensuring your private keys are never exposed to the computer or browser.
Quick Terms
Seed: your recovery phrase (secure & offline).
PIN: device unlock code.
Passphrase: optional extra security layer.
Stylized Login Flow
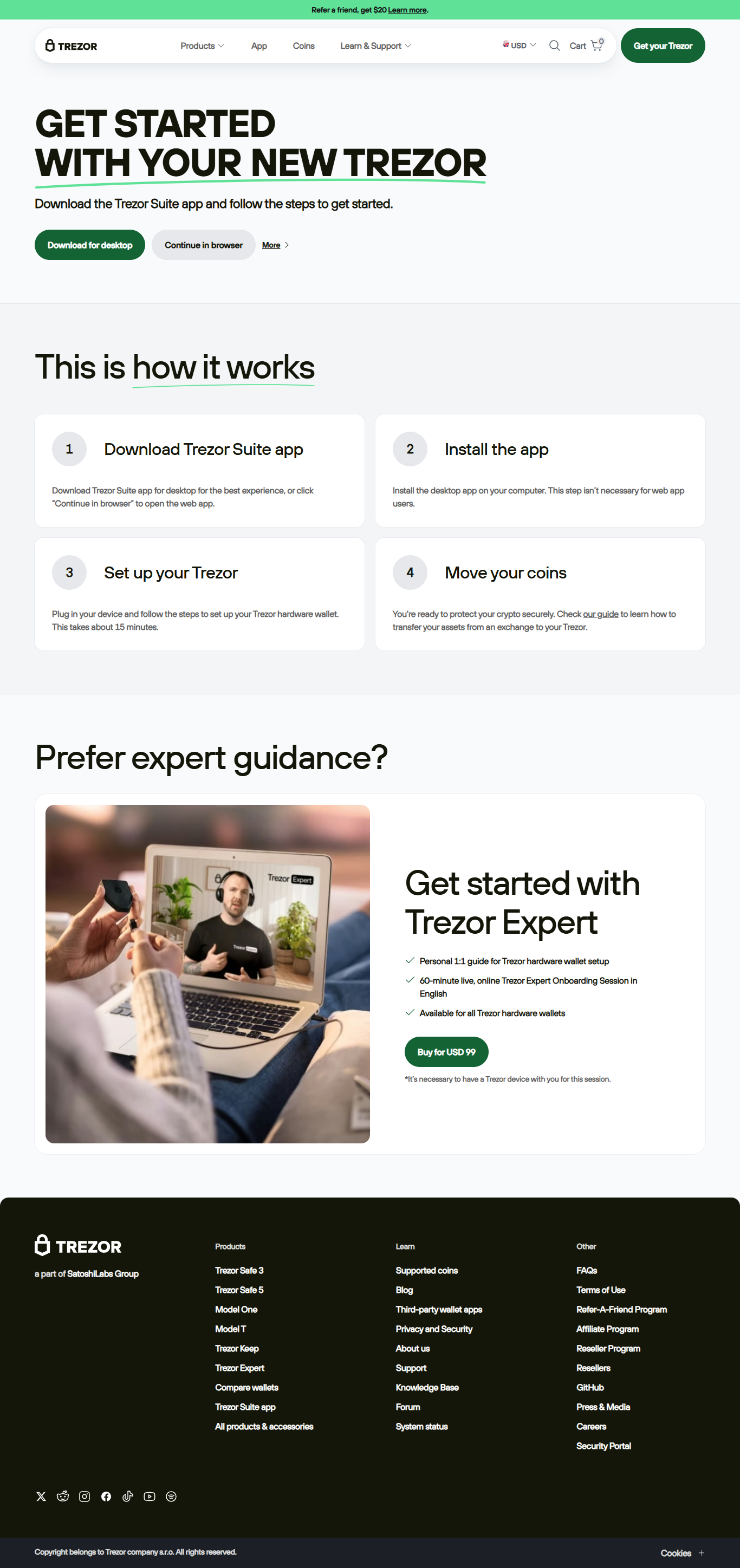
1 • Launch Suite
Open the Trezor Suite app or a compatible wallet. The app prepares a session for your device to join.
2 • Connect Physically
Attach the device via USB (or use supported bridge). The Suite detects and initiates a handshake with the device’s secure chip.
3 • Enter PIN
Use the device screen to enter your PIN. PINs are never entered into the host system — this prevents remote capture.
4 • Confirm Actions
Every signature or address approval is displayed on-device. Confirm visually; the host only sees approved transactions, not keys.
This multi-step approach turns login into a deliberate, verifiable ritual — attackers can’t fake approvals unless they have your hardware plus your PIN.
Login Shield — Visual Metaphor
The page uses a "shield" motif — soft neon rings animate around the device icon (conceptual, not scripted) — to reinforce the idea that authentication is a physical confirmation, not just a password exchange.
⟲
Human-Centric Flow
Designed so users trust the process visually before they act.
Quick Comparison: Login Models
Aspect
Trezor (Device)
Password-only
Key storage
Offline (secure chip)
Server/cloud
Action approval
On-device visual confirm
Hosted prompt
Remote risk
Minimal
High
Before You Login
- Install Suite from the official website (verify address).
- Keep firmware & app updated.
- Check browser extensions and disable suspicious ones.
During Login
- Connect device; confirm device model on screen.
- Enter PIN only on the device; never on the host.
- Verify the first/last characters of addresses before approving.
After Login
- Lock your session when idle.
- Revoke dApp approvals periodically.
- Keep recovery phrase offline and duplicated in secure places.
FAQ — Fast Answers
Q: Can I log in without the device?
A: Critical operations need the physical device for signatures. Some read-only features may be available, but full control requires the Trezor unit.
A: Critical operations need the physical device for signatures. Some read-only features may be available, but full control requires the Trezor unit.
Q: What if the device is not detected?
A: Try another USB cable/port, ensure Suite is up to date, and check for OS-level driver prompts. Reboot if necessary.
A: Try another USB cable/port, ensure Suite is up to date, and check for OS-level driver prompts. Reboot if necessary.
Q: Is the recovery seed stored anywhere online?
A: Never. The seed is generated on-device and should be recorded offline by you — it’s the only way to recover assets if the device is lost.
A: Never. The seed is generated on-device and should be recorded offline by you — it’s the only way to recover assets if the device is lost.
Final Thought
Treat login as a deliberate, secure step — a short ritual that preserves long-term control. When the device lights up and the screen asks for confirmation, pause and verify: that moment is your strongest defense.
Authenticate physically. Approve visually. Own your keys.
Tags: hardware wallet • PIN • recovery seed • on-device confirmation • self-custody